Privacy¶
Introduction¶
The Aspecto platform uses a graphical user interface web management interface for all components available to the user. This reference guide describes the menus and options associated with the Privacy function in the platform's web management interface.
Organization of the Manual¶
This manual contains the following chapters and appendix:
-
Data Classification
This chapter describes the Data Classification menu. It describes how to generate, view and process the data.
-
APPENDIX A - Glossary
This appendix defines the technical terms in this manual.
Changes in This Revision¶
- Updated all screens in data classification
Data Classification Summary Page¶
Path: Privacy > Data Classification
The Data Classifier should automatically start running when you first select that option. The first time the classifier runs it can take an hour or more to process, depending on the number of statements in the system. Once the classifier has completed the first pass it will continuously update every 10 minutes.
Once the classifier has run to completion, the Data Classifier summary screen will appear.
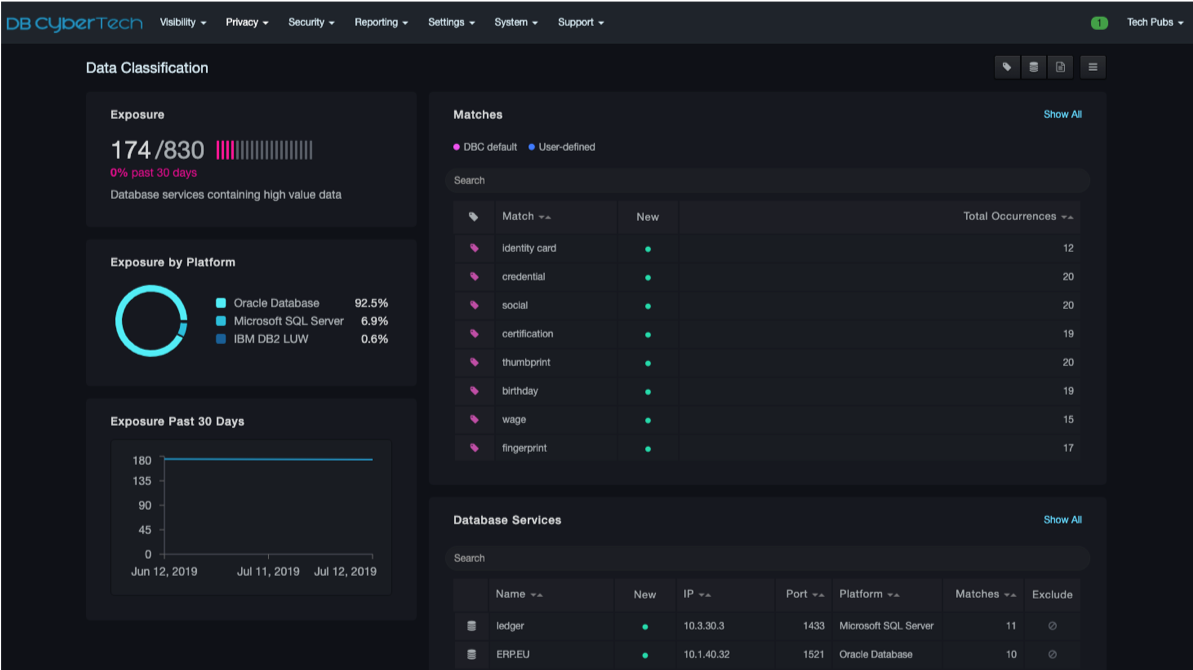
The Data Classification summary page presents the user with a view of PII exposure, quantified by total services identified and by database platform. This shows the services in which SQL statements were discovered to be processing personal data.
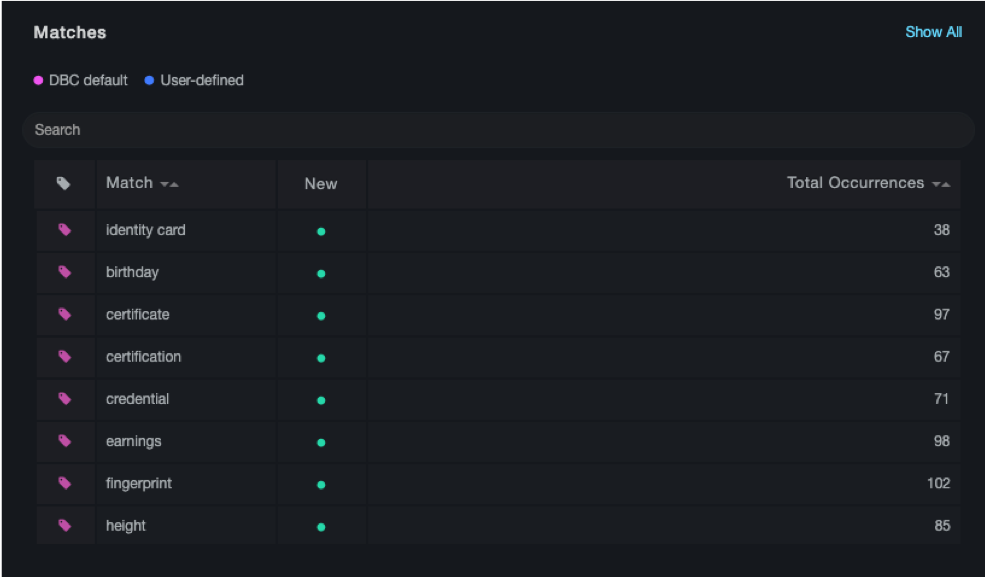
On the top right side of the summary page, the system displays the terms matched and total occurrences identified. Selecting a term will take the user to a detail page.
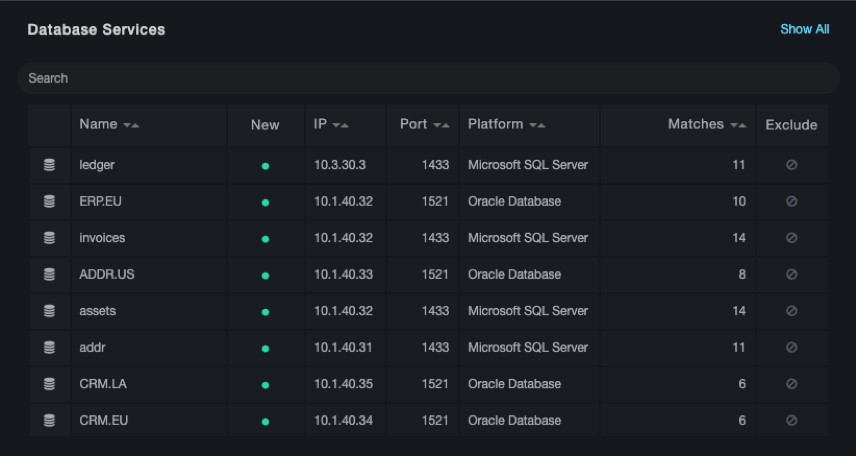
At the bottom right of the summary page, a list of the database services with PII data is displayed. Selecting a database service will take the user to a detail page.
Data Classification Drill Downs¶
Match Drill Downs¶
The user can select a matching term and the system will display the list of databases containing that term, along with the time frame the term was used in SQL queries.
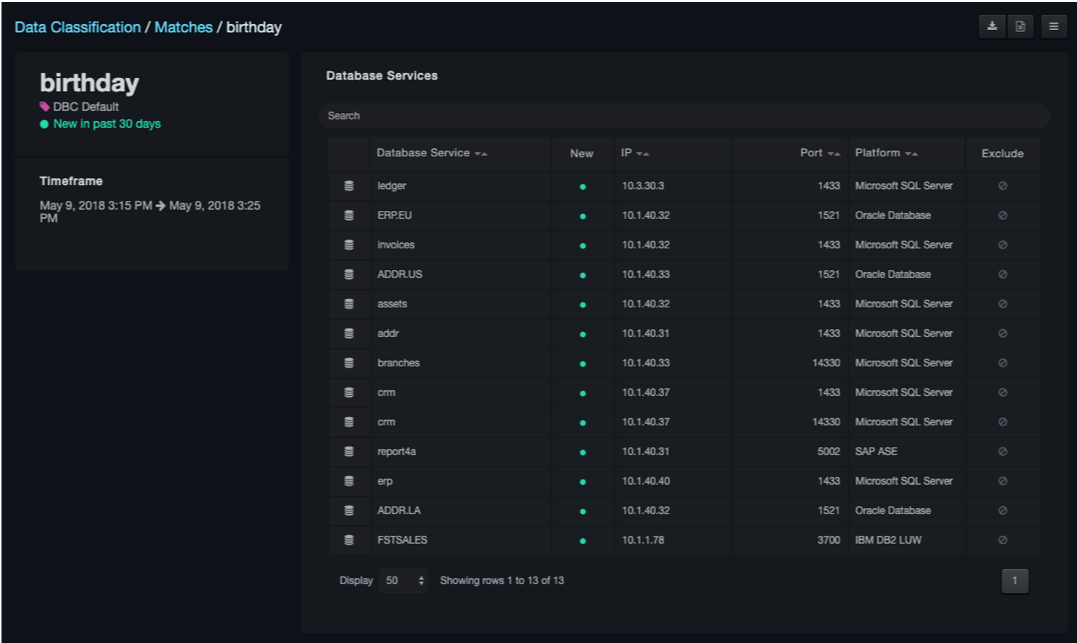
The user may select an individual database service from this screen to be taken to the service drill down page.
Service Drill Downs¶
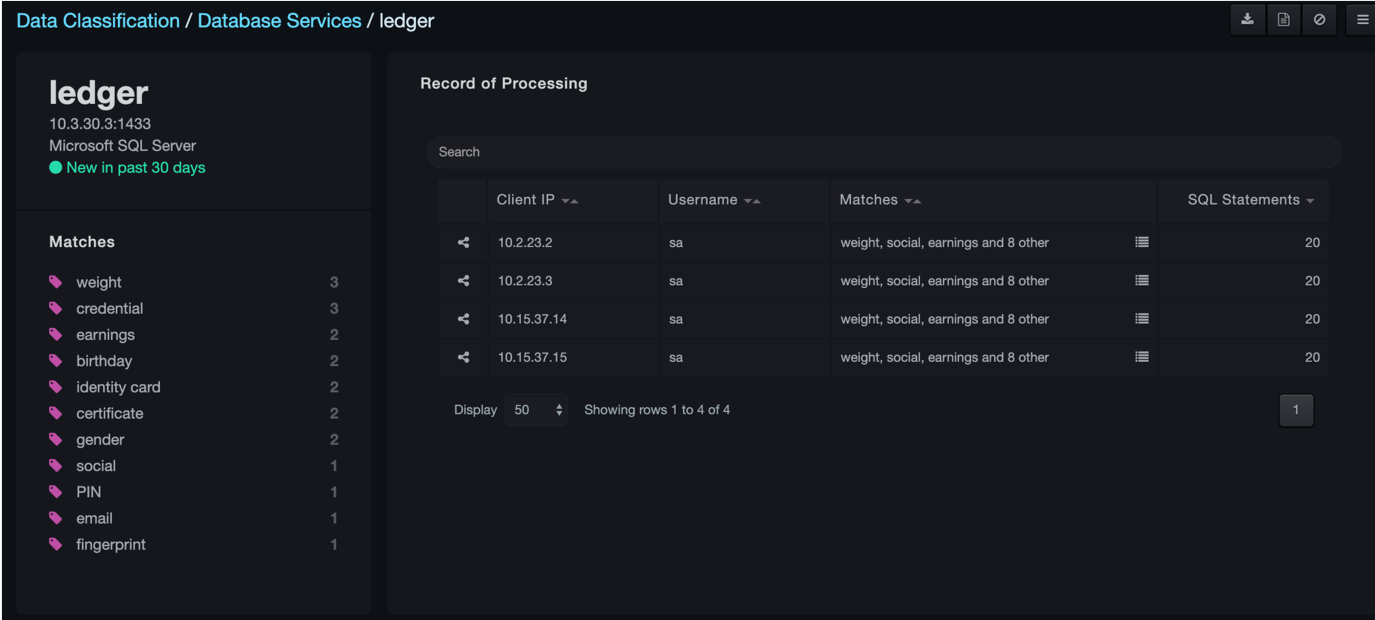
Selecting a service displays a new detail page about the indicated service.
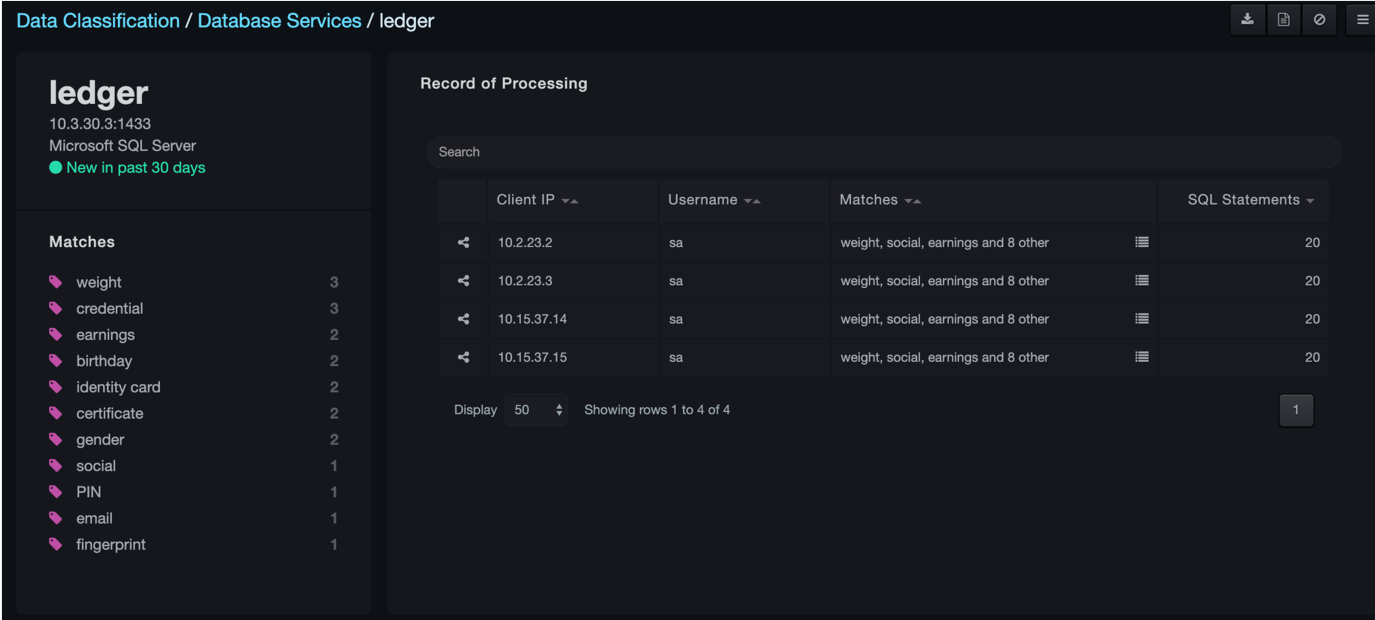
On the left side of the page is a list of all terms identified for the selected service. Clicking on a match will take the user to the match drill down page for the selected item.
On the right side of the page is a record of all clients connecting to the service along with the matched terms.
Columns in the Database Services page
| Column | Description |
|---|---|
| Client IP | IP address that the client is using. |
| User Name | User name that the connection statement is using. |
| Matches | Related terms that the statements are grouped by. |
Data Classification Options¶
The options bar provides options for exporting matches or services via CSV, or a summary PDF report.
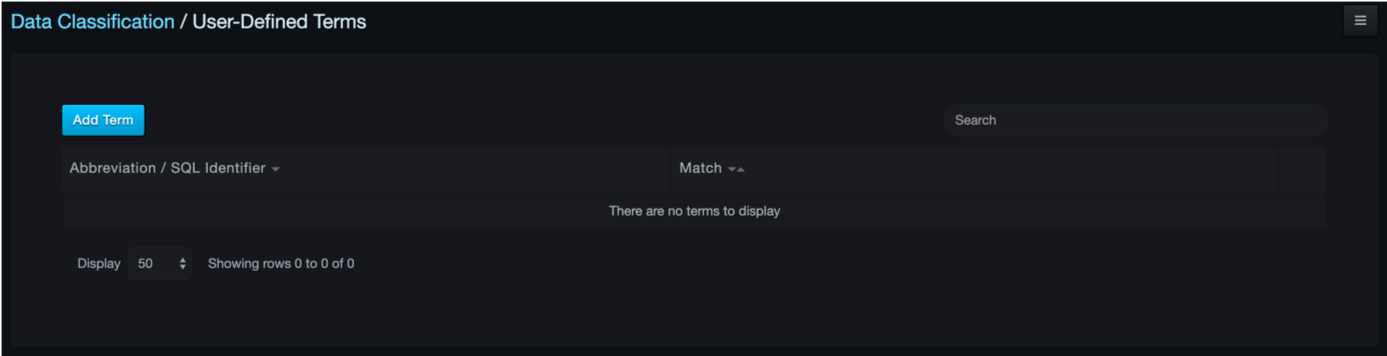
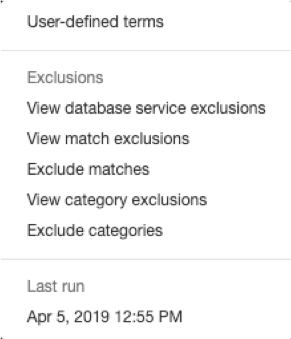
User-Defined Terms¶
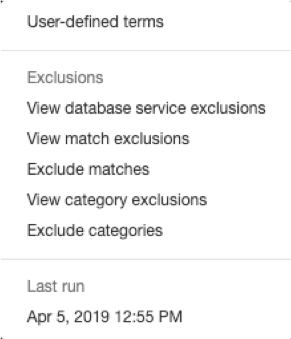
By selecting the  icon on the very right-hand
side of the summary page, the user can select the User-Defined
Terms option from the dropdown menu to access the terms associated with the classifier.
icon on the very right-hand
side of the summary page, the user can select the User-Defined
Terms option from the dropdown menu to access the terms associated with the classifier.
You can add terms (letter groupings, words, or phrases) for the classifier to identify while it runs.
To add a new term, select Add Term.
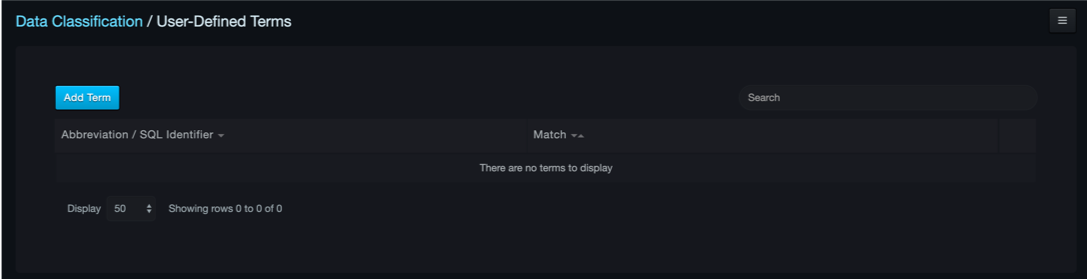
Then, select the appropriate option for the new term.
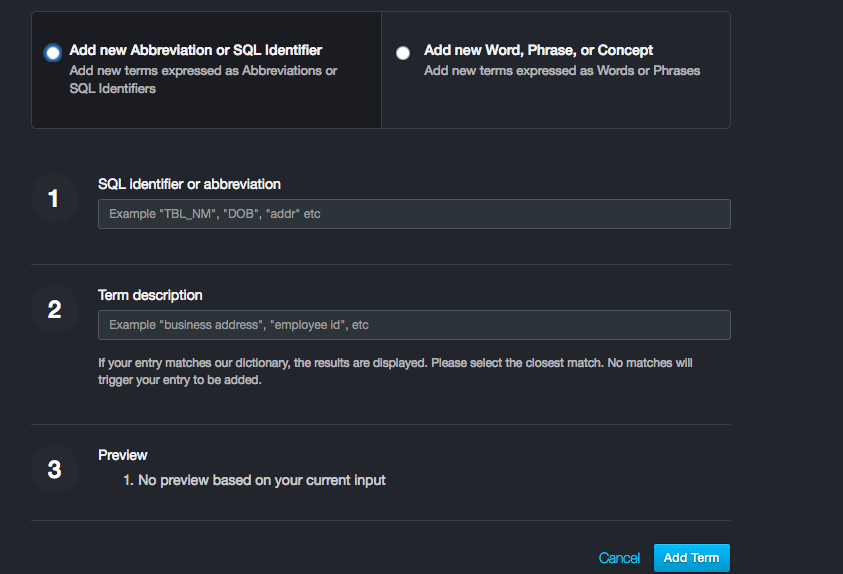
Add New Abbreviation or SQL Identifier to Classifier¶
By selecting Add New Abbreviation or SQL Identifier, you are choosing for the Classifier to look directly into the SQL statements for matches.
You first need to add the exact identifier or abbreviation for the Classifier to find in the first dialog box, then add the description of what kind of information the term is associated with.
Add New Word, Phrase, or Concept to Classifier¶
By adding a new word, phrase, or concept as a new term, this will tell the Classifier to look at only the description of the term and match it with the statements, not directly looking into the SQL statements themselves. This gives the Classifier more flexibility to look at terms more broadly in the databases instead of exact matches in the SQL statements.
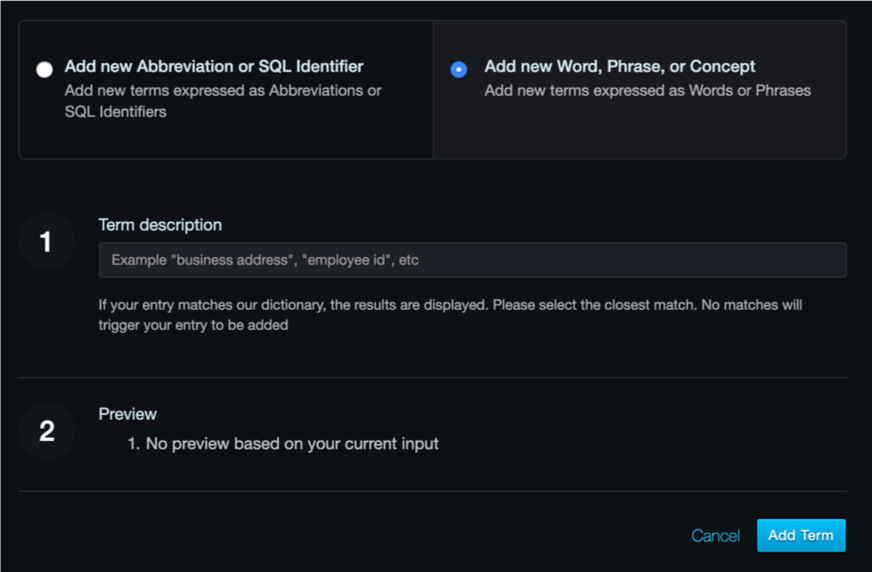
When finished adding the term description, select Add Term.
Exclusions¶
Directly under User-Defined Terms option are the Exclusion options. Services, matches, or categories may be excluded from the classifier and resulting reports.
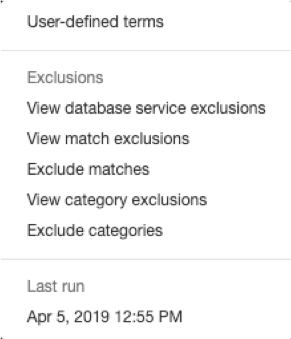
Selecting an exclusion option will take the user to an empty screen, similar to the following:
Excluding a Service from a Report¶
To exclude a database service result, go to the summary page and select the service that you want to exclude.
Then, in the top right hand corner, click the  icon.
icon.
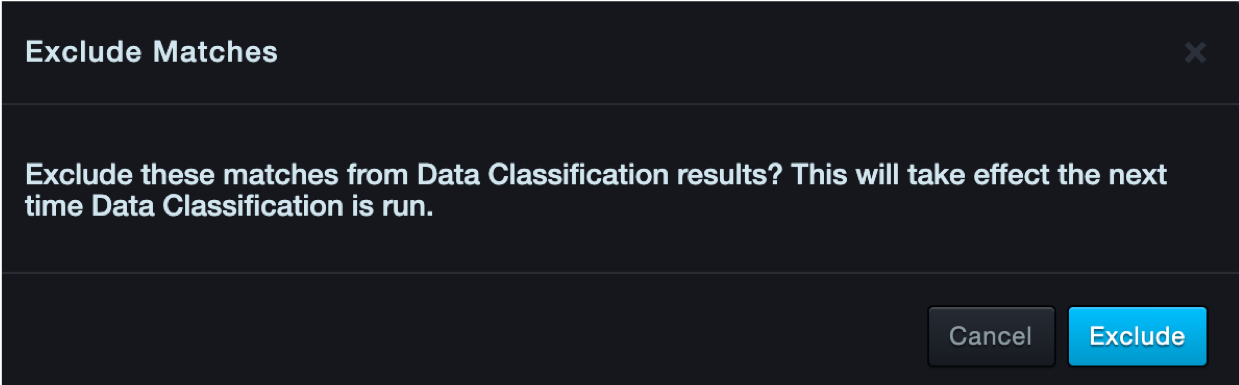
The following message will appear:
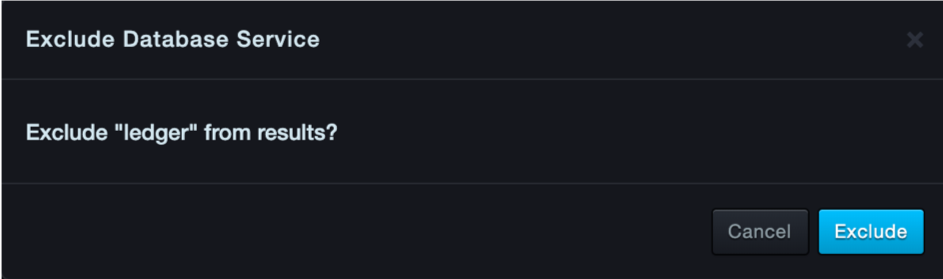
Click Exclude.
Now using the designated pathway again you will now see the service you just excluded from results.
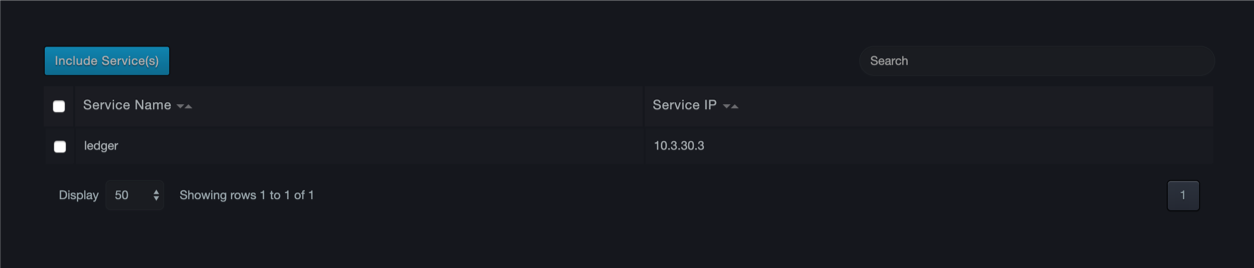
Re-Add a Service¶
To add the service back into your results, click the box to the left of the service and click Include Service.
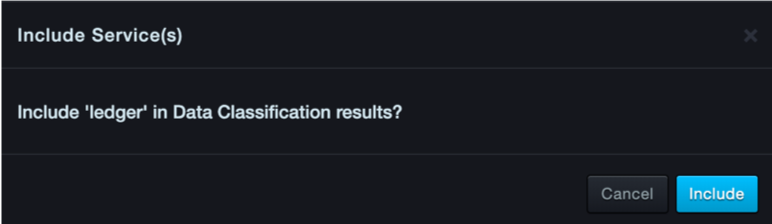
Click Include. Then the service will be included back into your classifier results.
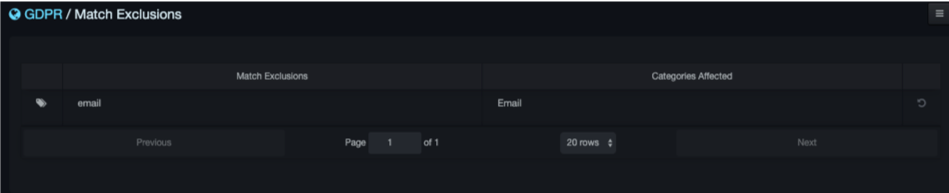
Excluding Matches from a Report¶
The system allows the user to exclude specific matches if desired.
Select Exclude matches to be taken to the configuration screen. The system will generate a list of recommended match exclusions based on the quality of the matches found during discovery.
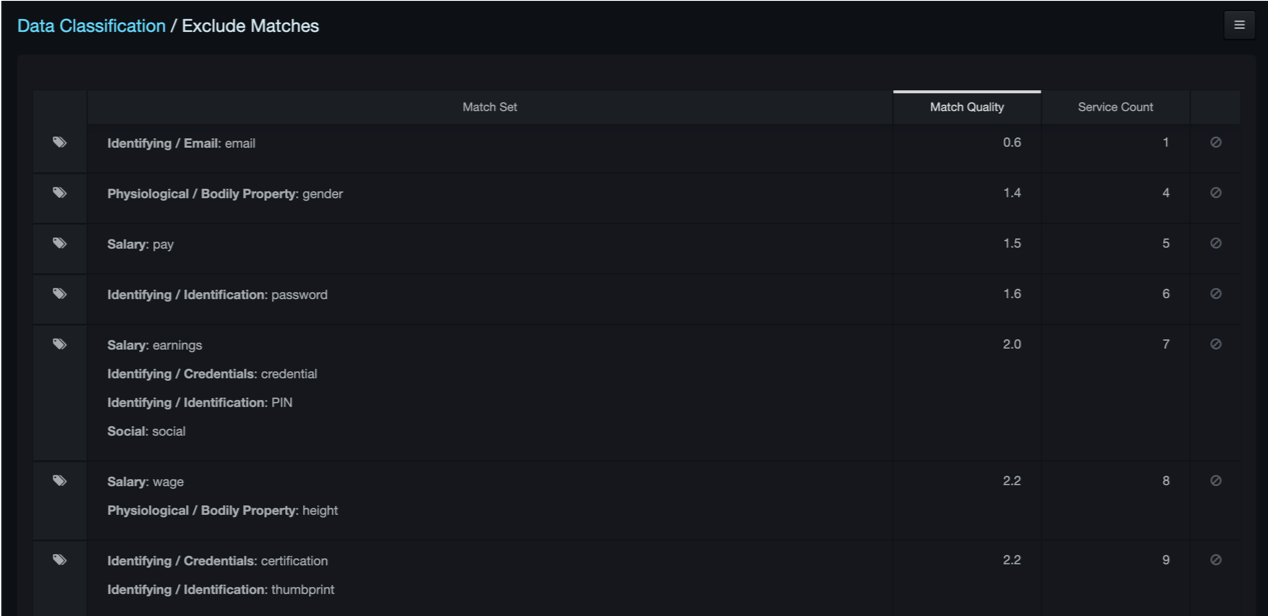
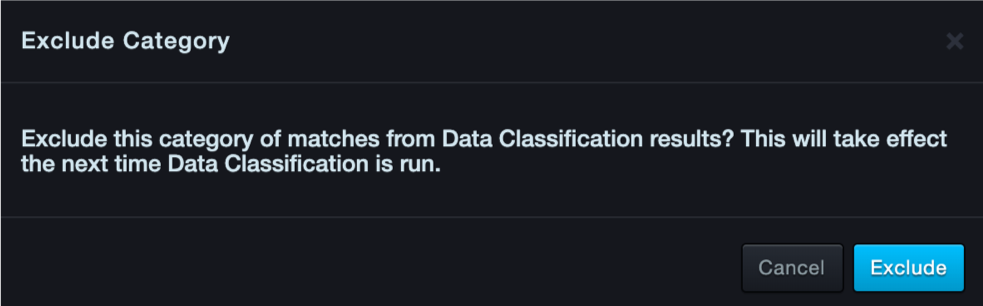
Click on the exclude button  on the right side of the match to exclude it from the classifier. The system requires confirmation, select Exclude.
on the right side of the match to exclude it from the classifier. The system requires confirmation, select Exclude.
The classifier must run again before the exclusions can be viewed.
Once complete, the user may view the excluded matches.
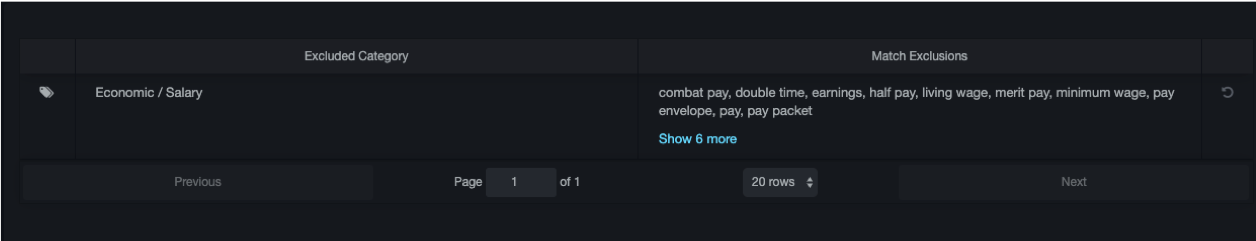
Excluding Categories from Report¶
The system allows the user to exclude categories of matches if desired.
Select Exclude categories to be taken to the configuration screen. The system will present the various categories of matches that can be excluded.
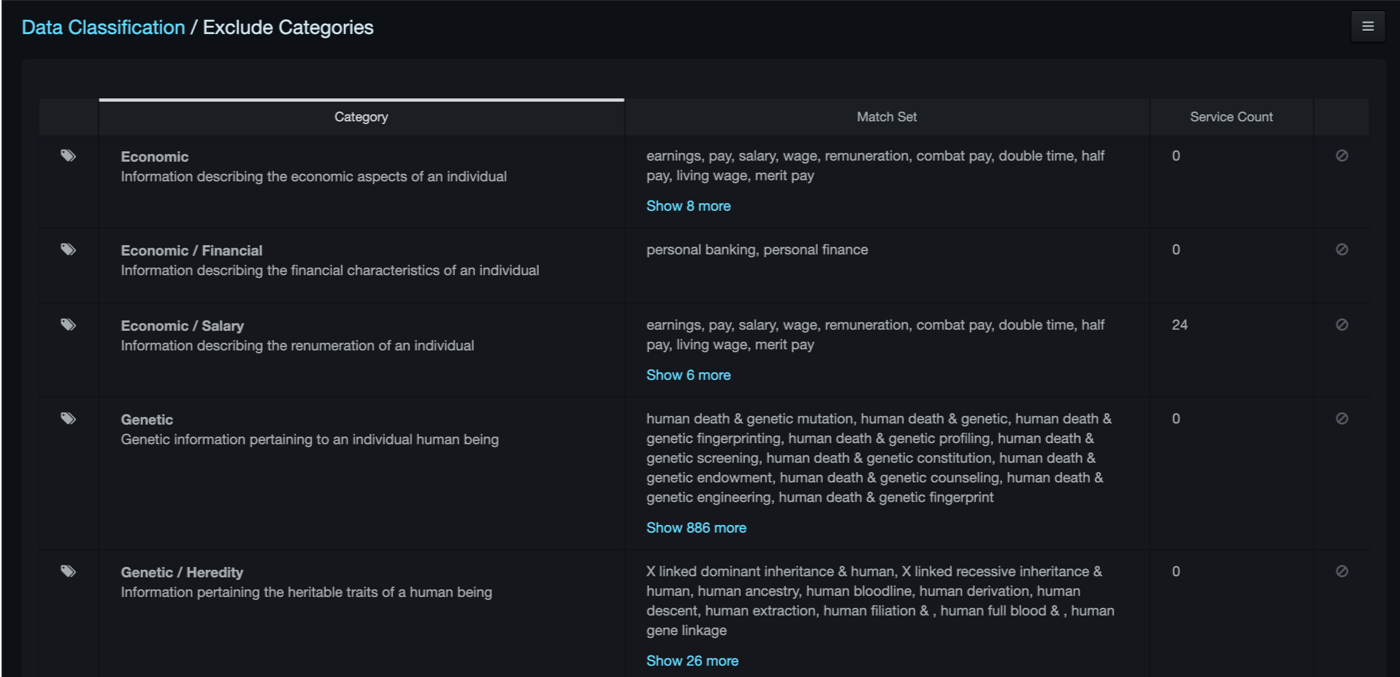
Click on the exclude button  on the right side of the category to exclude it from the classifier. The system requires confirmation, select Exclude.
on the right side of the category to exclude it from the classifier. The system requires confirmation, select Exclude.
The classifier must run again before the exclusions can be viewed.
Once complete, the user may view the excluded categories.
Contact Technical Support¶
For any technical difficulties you may experience, you can contact DB CyberTech Technical Support at the following:
Email: support@dbcybertech.com
Phone: 1(800) 375-0592
Glossary¶
| Term | Definition |
|---|---|
| API | Application Programming Interface. A set of routines, protocols, and tools for building software applications. |
| Blacklisted statements | Statements that are not added to the learned set. Typically, these statements are used to filter out benign statements generated by DBAs or other non-application related interactions |
| BPF | Berkeley Packet Filter. An architecture for user-level packet capture. BPF provides a raw interface to data link layers in a protocol-independent fashion. |
| CAC | A "smart" card about the size of a credit card used as identification for active duty uniformed service personnel, Selected Reserve, DoD civilian employees, and eligible contractor personnel. |
| CSV | Comma-separated value. Data format where each piece of data is separated by a comma. |
| DHCP | Dynamic Host Protocol Configuration. A standardized network protocol used on Internet Protocol networks to dynamically distribute network configuration parameters, such as IP addresses, for interfaces and services. With DHCP, computing devices like your DBC platform request IP addresses and networking parameters automatically from a DHCP server, reducing the need to configure these settings manually. |
| DNS | Domain Name System. A hierarchical decentralized naming system for computers, services, or any resource connected to the Internet or a private network. DNS translates domain names into the numerical IP addresses to locate and identify computer services and devices with the underlying network protocols. |
| LDAP | Lightweight Directory Access Protocol. A protocol for accessing a directory listing in a TCP/IP network. It is a sibling protocol to HTTP and FTP and uses the ldap:// prefix in its URL. |
| Learned set | Contains statements considered to be part of the application’s normal behavior. |
| MAC | Media Access Control. A hardware address that uniquely identifies each node of a network. |
| MTU | Maximum Transmission Unit. The largest physical packet size measured in bytes that a network can transmit. Any messages larger than the MTU are divided into smaller packets before being sent. |
| Network File System | A client/server application that allows network users to access shared files stored on computers of different types using a Virtual File System that runs on top of TCP/IP. |
| NTP | Network Time Protocol. A networking protocol for clock synchronization between computer systems over packet-switched, variable-latency data networks. |
| pcap | Short for packet capture. A program for capturing network traffic. |
| Server Message Block | A message format used by Windows to share files, directories, and devices. |
| SSL | Secure Sockets Layer. A protocol for transmitting private documents via the Internet. SSL uses a cryptographic system that uses two keys to encrypt data. |

DB CyberTech
15015 Avenue of Science
Suite 150
San Diego, CA 92128
http://www.dbcybertech.com